AIS spoofing vs GNSS interference: Why the distinction decides the claim
The signal looks the same. The response is entirely different.
Every underwriter working in marine hull and war risk has, by now, encountered vessels that appear to teleport across the chart, hold a static position while their physical track diverges, or cluster improbably with dozens of other ships at a single offshore waypoint. Position anomalies are no longer exceptional events. They are, increasingly, the background noise of global maritime trade.
But not all position anomalies are the same. The failure to distinguish between them — at placement, at renewal, and above all at claims — is one of the more consequential analytical errors circulating in the market today.
There are three distinct signal failure types. One is deliberate and vessel-originated. Two are external and vessel-agnostic. The insurance implications of each are radically different, and the clauses that respond to them sit in entirely separate parts of the policy.
Getting the taxonomy right is not a technical nicety. It is the difference between a claim that pays and a policy that voids.
The three signal types: A working definition
AIS spoofing is an active, vessel-originated manipulation. The vessel — or an operator acting on its behalf — manipulates the AIS transponder to broadcast a false position. The vessel's own GPS may be accurate; only the broadcast is falsified. The lie is deliberate and directional. The vessel is the actor.
GNSS jamming is passive interference. An external RF noise source overwhelms satellite signals in a given area. Affected receivers lose lock and raise an alarm. The failure is visible — the navigator knows something is wrong.
GNSS spoofing is the more operationally dangerous of the two passive types. An external actor broadcasts counterfeit satellite signals. The GNSS receiver locks onto a plausible but incorrect position, with no alarm raised. The navigator has no indication that the position data is compromised. The failure is invisible.
The operational and legal distinction between active and passive is not subtle. In the active case, the vessel is the problem. In the passive case, the vessel is the victim. The insurance response is entirely different, and the clauses that govern each are not interchangeable.
Why the active/passive distinction is so consequential
When a vessel actively manipulates its AIS broadcast, the claim lands immediately in underwriting and sanctions territory.
A false position broadcast is capable of constituting material misrepresentation under the duty of utmost good faith — the uberrimae fidei principle enshrined in MIA 1906 s.17. Where the broadcast is sustained and deliberate, an insurer has grounds to argue that cover is voided, not merely suspended. Section 55(2)(a) of the same Act provides that an insurer is not liable for loss attributable to the wilful misconduct of the assured — and deliberate position manipulation is difficult to characterise as anything else.
Beyond coverage, there is the sanctions dimension. A Kpler analysis of maritime sanctions data showed that 80% of vessels that exhibit active AIS spoofing behaviour are designated within twelve months. That is not a statistical curiosity. It is an underwriting signal. A vessel that is spoofing today is, with high probability, a sanctions exposure tomorrow. The practical response for H&M and P&I underwriters is to decline, reprice, or exit the relationship — and to do so before designation, not after.
The AIS operational warranty, increasingly written into H&M policies, formalises this exposure. It requires continuous, accurate AIS transmission as a condition of cover. Where a vessel is found to have suppressed or falsified its broadcast, the warranty is broken — and cover falls away regardless of what caused the loss.
Active spoofing: The scale of the problem
The scale of active AIS manipulation has moved well beyond isolated, opportunistic deception. AIS spoofing incidents are running at 25 times the 2023 baseline. The same data set records 261 vessels that were found to have been spoofing prior to being sanctioned — confirming that position manipulation is functioning as a precursor and enabler of sanctions evasion, not merely a symptom of it.
Four behavioural signatures are now well established in the detection literature:
- Circular loop: The vessel appears to orbit a fixed geographic point at speeds that are physically impossible for any commercial vessel type.
- Teleportation: The AIS track shows the vessel jumping hundreds of nautical miles within minutes.
- Static ghost: The AIS position is frozen while the vessel continues to move. The broadcast position and the vessel's actual track diverge.
- Identity clone: Two vessels broadcast the same MMSI identity simultaneously. One track is real; one is fabricated.
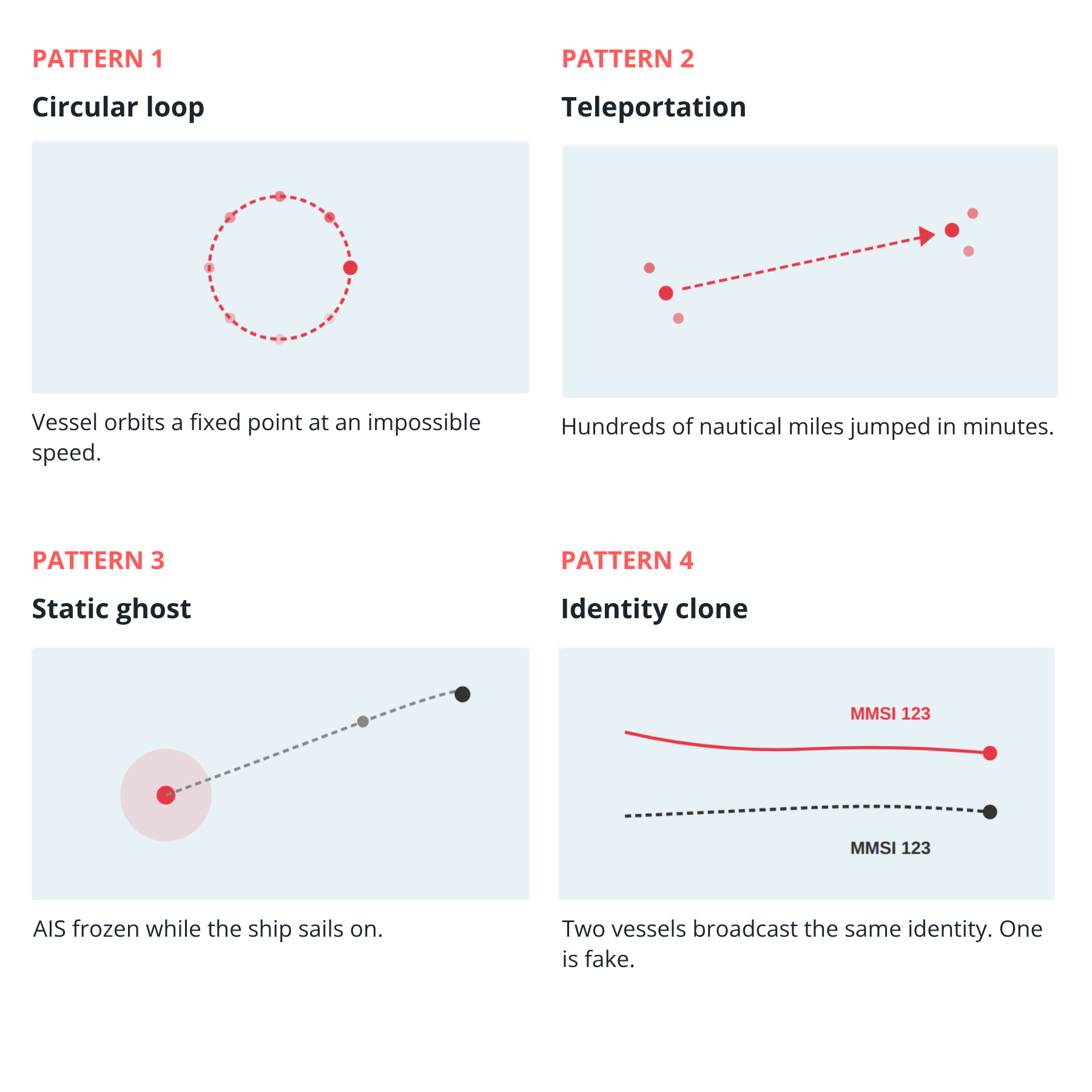
Each of these patterns is identifiable from the signal data alone, without reference to any other source. In combination with sanctions watchlists, ownership registers, and port state control records, they form the evidential basis for an underwriting decision — or, in a claims context, a coverage argument.
The passive problem: One signal, many victims
GNSS jamming and spoofing operate on a fundamentally different geometry. Where active AIS manipulation affects a single vessel by design, passive GNSS interference affects every receiver within range of the emission source simultaneously. The signature is diagnostic: multiple vessels in the same area report convergence on a single false position, often a land-based point well inland of their actual location.

Six major maritime corridors are currently active:
- Persian Gulf and Strait of Hormuz
- Eastern Mediterranean
- Black Sea
- Baltic Sea and Gulf of Finland
- Red Sea and Gulf of Aden
- Bay of Bengal and Myanmar coast
Every major corridor is now affected, and the numbers are accelerating, with more than 24,000 vessels affected globally across 2025. Since February 2026 alone, more than 1,650 disruptions have been recorded in the Gulf region. The coverage implications here are distinct from the active case — and, for the vessel, considerably more favourable.
GNSS interference originating from state or state-proximate actors falls within the scope of the Institute War & Strikes Clauses (IWSC). The vessel is not the perpetrator; it is the victim of an external act that has been assessed as falling within the covered war peril. JWC Listed Area designation applies — hull war cover is repriced via the Additional War Risk Premium (AWRP), charged as a percentage of hull value per seven-day exposure. Underwriters retain the right to cancel and re-rate war cover at seven days' notice under IWSC Clause 5.
The Cyber Clause (CL.380 / LMA 5403) is increasingly invoked where electronic interference is treated as a cyber peril rather than a war peril. The characterisation matters: it affects not only coverage routing but premium allocation, aggregation management, and reinsurance recovery.
The claims reconstruction challenge is significant. Because the vessel's GPS was compromised, AIS track data is evidentially unreliable for the incident period. VDR records, non-GPS positioning streams, and independent surveillance data carry the evidentiary weight. Claims that rely solely on AIS track data from a spoofed period are, accordingly, vulnerable.
What actually confirms where the ship was
The question that sits at the centre of every spoofing-related claim — whether active or passive — is the same: where was the vessel, and what evidence establishes that?
AIS alone cannot answer this question in a contested spoofing case. Four independent data layers, each weakest alone and strongest in combination, are now standard in serious claims reconstruction and underwriting due diligence:
- Terrestrial and satellite AIS with plausibility checks applied across receivers. Impossible speeds, impossible jumps, and duplicate identities are caught at signal level when multi-source data is cross-referenced. Single-source AIS is not sufficient.
- SAR and optical satellite imagery provides independent visual confirmation of true vessel position, regardless of what the AIS broadcast showed. It is the only data source that physically locates the vessel in space and time, independent of any radio signal.
- RF geolocation locates a vessel by triangulating its radio emissions — its true RF signature — even when the AIS broadcast is suppressed, falsified, or absent. Where AIS is off or manipulated, RF geolocation can establish a factual position independent of the declared one.
- Human intelligence — shoreside photography, port agent records, crew testimony, and physical sightings — provides ground truth when electronic signals are compromised or contested. It is low-tech and often decisive.
.png)
None of these sources is individually sufficient to resolve a contested case. In combination, they construct a position narrative that can withstand forensic scrutiny — and which an arbitration panel or court can assess against the coverage argument.
The clauses that govern each scenario
The policy architecture for active and passive spoofing sits in entirely different contractual locations.
.png)
For active AIS manipulation, the relevant provisions are MIA 1906 s.17 (utmost good faith and the materiality of false position broadcasts), s.55(2)(a) (exclusion of loss from wilful misconduct), the Sanctions Clause (LMA 3100 / JH 2010/009) which suspends cover automatically upon OFAC, EU, or UK designation, the AIS operational warranty, and ICC (A) Clause 4.1 which excludes cargo cover attributable to the wilful misconduct of the assured.
For passive GNSS interference, the operative framework is the Institute War & Strikes Clauses, JWC Listed Area provisions and the AWRP mechanism, IWSC Clause 5 on seven-day cancellation rights, and the Cyber Clause where electronic interference is classified as a cyber peril rather than a war risk. Claims reconstruction rests on non-AIS evidentiary sources, because the AIS record from the affected period is unreliable by definition.
The practical implication is that the underwriter or adjuster who treats a GNSS spoofing event as if it were an AIS spoofing event — or vice versa — is working from the wrong clause set, the wrong coverage question, and the wrong evidential standard. The preliminary classification step is not administrative. It is substantive.
What this means for underwriting practice
Position anomalies will continue to increase. The structural drivers — sanctions pressure, geopolitical contestation of key corridors, the proliferation of electronic warfare capability — are not abating. The six affected maritime corridors identified above span the majority of global trade volume. Spoofing is no longer an exceptional risk in a handful of jurisdictions; it is a baseline operating condition across the international fleet.
For underwriters, the implication is that AIS track data should be treated as a starting point for risk assessment, not a conclusion. A clean AIS history is not the same as a clean operational history. The four spoofing signatures — loop, jump, static ghost, clone — are detectable from the signal record and should be screened at inception and renewal, not only when a claim arises.
For claims professionals, the implication is that the preliminary determination of active versus passive — vessel as actor or vessel as victim — must precede the coverage analysis. The data sources that can make that determination are available; the question is whether they are being systematically applied.
The market has the contractual tools to manage this exposure. The Institute clauses, the AIS warranty, the JWC mechanism, and the Cyber Clause together provide a framework that is coherent, if applied correctly. The gap is not in the policy language. It is in the classification step that determines which part of the policy applies.
Three signals. Not the same.

See why the most successful traders and shipping experts use Kpler